Dive into the fascinating world of aircraft tracking with our comprehensive guide on Dump1090. Whether you’re an aviation enthusiast, a professional in the field, or simply curious about the technology…

Capturing evidence from a remote system using SSH may be easier than you think.

We delve into the clandestine world of Crime as a Service, a phenomenon transforming the landscape of cybercrime. Through an engaging narrative, the article explores how CaaS has created a…

In an era where digital footprints are closely monitored, Lokinet emerges as a revolutionary cloak of invisibility, enabling users to traverse the online world unseen. Paired with Oxen, a cryptocurrency…

The specter of Advanced Persistent Threats (APTs) casts a long shadow over organizations worldwide. These digital adversaries, often state-sponsored entities, employ a level of sophistication and stealth that traditional security…

With the CSIL-COA OSINT certification, you’re not just learning to navigate the digital realm; you’re mastering it. This course is a deep dive into the core of online investigations, blending…
A covert channel is a type of communication method which allows for the transfer of data by exploiting resources that are commonly available on a computer system. Covert channels are…
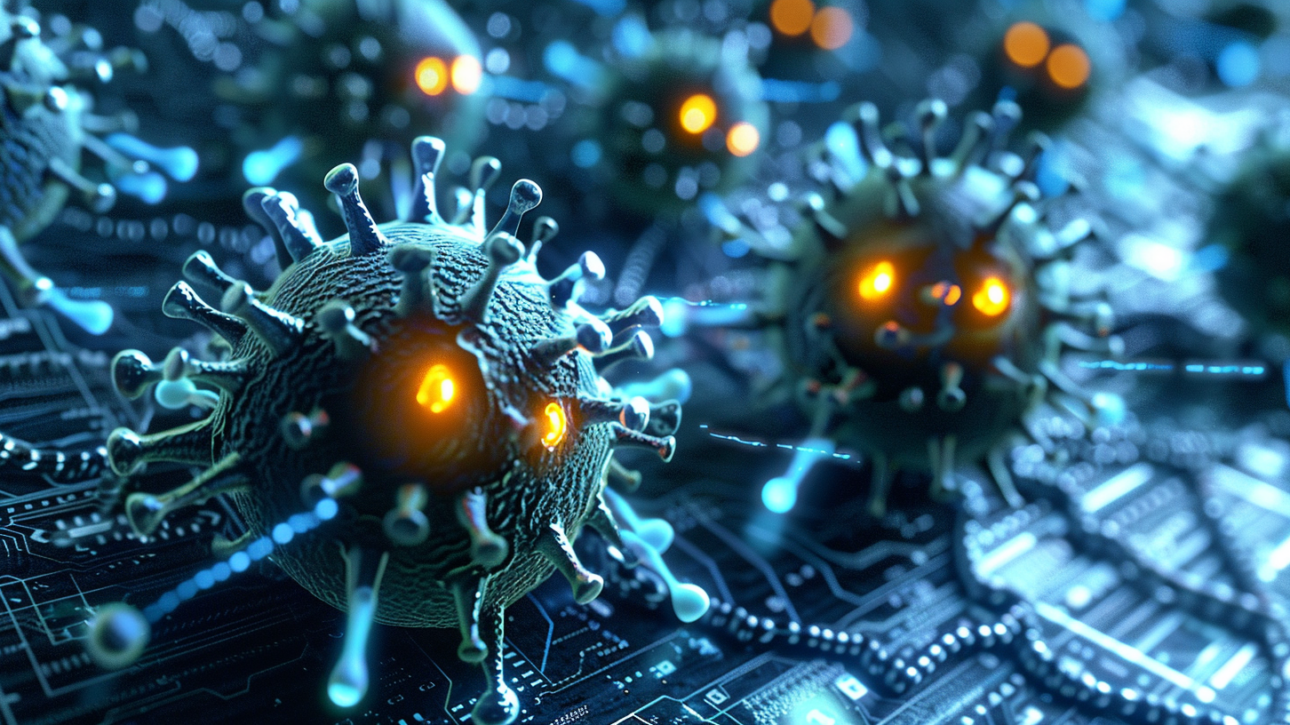
Dynamic malware analysis is a technique used to analyze and understand the behavior of a malware sample by running it in a controlled environment and observing its actions. This technique…

Unlock a FREE cybersecurity certification on us! Have you ever wondered how CSI Linux differentiates itself from other Linux distributions? This is your chance to dive in.
CSI Linux is…

Our exploration into the perils of contaminated digital evidence sheds light on scenarios that are not mere fabrications but real-world possibilities that could unravel the fabric of a meticulously built…